Introduction
Attribution in cyber threat intelligence has long been built around the concept of persistent adversary groups commonly labeled as Advanced Persistent Threats (APTs). These designations, widely used by organizations such as MITRE and leading threat intelligence vendors, attempt to cluster malicious activity under unified identities based on observed behaviors, infrastructure, and tooling. However, this model increasingly faces structural limitations in modern threat landscapes.
In reality, APT groups are not static entities. They evolve continuously operators rotate, development teams shift, tooling is replaced, and operational objectives adapt to geopolitical priorities. This creates a fundamental challenge: if the underlying components of a threat group change over time, on what basis can its identity persist? This dilemma closely mirrors the classical philosophical paradox known as the Ship of Theseus—if every part of a ship is replaced, is it still the same ship?
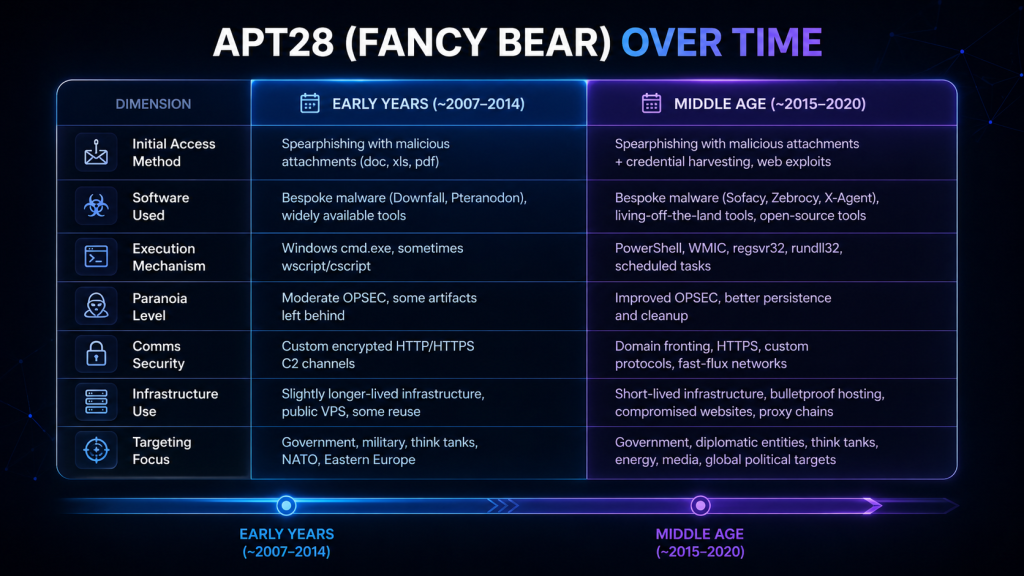
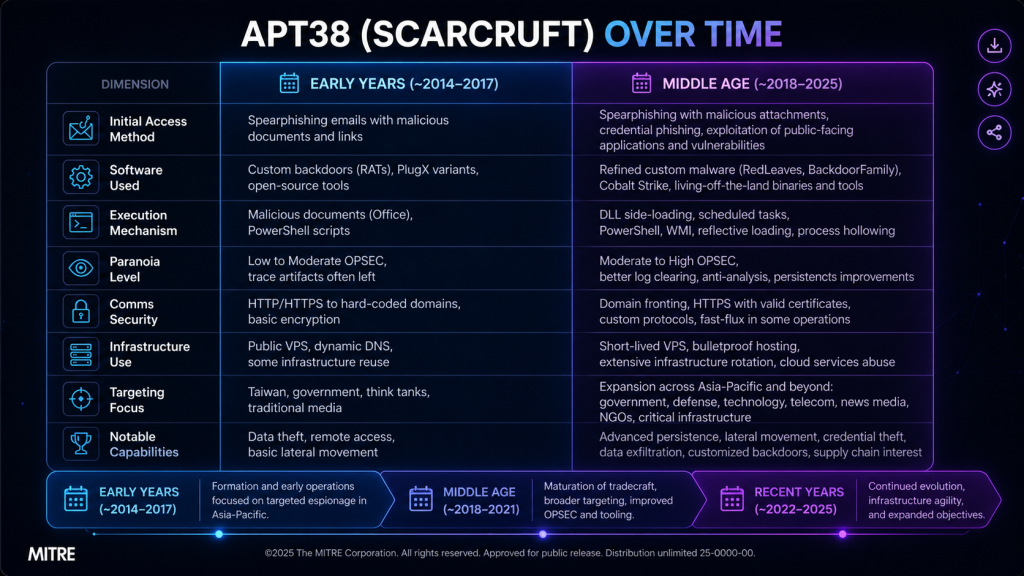
Traditional attribution methodologies have often leaned heavily on Tactics, Techniques, and Procedures (TTPs), as formalized in frameworks such as the MITRE ATT&CK. While TTPs provide a structured lens for understanding adversary behavior, they are not inherently stable identifiers. Threat actors can deliberately modify their techniques, adopt publicly available tooling, or mimic the tradecraft of other groups to evade detection and attribution. As a result, reliance on static TTP mapping alone introduces the risk of misattribution and oversimplification.
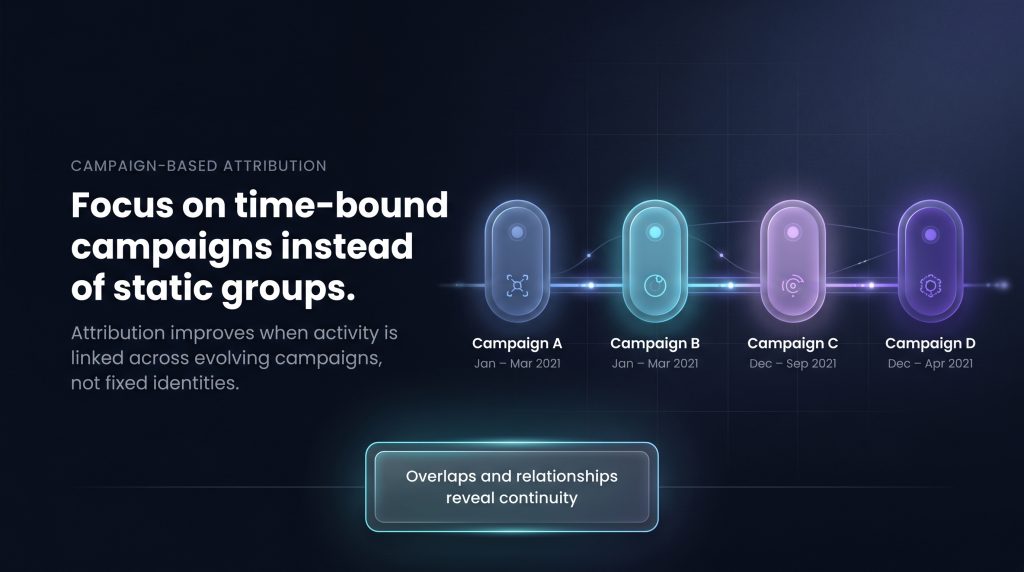
To address these challenges, modern threat intelligence practices are shifting toward a more dynamic model centered on campaign-based analysis. Rather than treating APT groups as fixed entities, analysts increasingly focus on discrete campaigns time-bound clusters of activity characterized by specific objectives, infrastructure, and operational patterns. By analyzing relationships and overlaps between campaigns over time, it becomes possible to infer continuity, evolution, and potential common sponsorship, even in the absence of identical TTPs.
Problem Statement
Attribution in cyber threat intelligence remains one of the most complex and contested challenges in modern cybersecurity. While organizations such as MITRE and commercial intelligence providers maintain structured profiles of Advanced Persistent Threat (APT) groups, these profiles are inherently built on evolving and often incomplete observations. The fundamental issue lies in the assumption that adversary groups represent stable, continuous entities, despite clear evidence that their composition, tooling, and operational behavior change over time.
This challenge introduces a critical paradox in attribution: if an adversary group replaces its operators, adopts new tools, modifies its infrastructure, and alters its Tactics, Techniques, and Procedures (TTPs), on what basis can analysts confidently assert continuity of identity? This dilemma reflects the philosophical concept of the Ship of Theseus, where the persistence of identity is questioned when all underlying components have been replaced.
How can threat intelligence practitioners accurately link and attribute adversary activity over time when group membership, tooling, infrastructure, and TTPs are subject to continuous change?
Traditional attribution models rely heavily on mapping observed activity to known TTPs, often structured through frameworks such as the MITRE ATT&CK. However, this approach presents significant limitations. TTPs are not exclusive identifiers; they can be deliberately modified, shared across groups, or adopted through publicly available tools and malware-as-a-service ecosystems. As a result, adversaries can evade attribution or even intentionally mislead analysts by mimicking the behaviors of other groups.

Moreover, the increasing commoditization of cyber capabilities ranging from exploit kits to phishing frameworks and command-and-control infrastructure further blurs the boundaries between distinct threat actors. This creates a landscape where multiple groups may exhibit overlapping behaviors, making it difficult to distinguish between genuine continuity and coincidental similarity.
Consequently, the core problem addressed in this research is the lack of a reliable, systematic approach for maintaining attribution continuity in the face of adversary evolution. Specifically, this research seeks to answer the following question:
Traditional Attribution and Its Limitations
Traditional cyber threat attribution has historically centered on the identification and tracking of adversary groups as relatively stable entities. Security vendors and frameworks such as MITRE formalize this approach by clustering observed activity malware, infrastructure, and Tactics, Techniques, and Procedures (TTPs) under designated group profiles within resources like the MITRE ATT&CK. This model assumes that consistent behavioral patterns can reliably represent a specific adversary over time.
At its core, traditional attribution relies on correlating newly observed activity with previously documented TTPs. When sufficient overlap is identified such as similar initial access vectors, persistence mechanisms, or command-and-control behaviors the activity is attributed to a known group. This method has proven valuable in establishing baseline understanding of adversary tradecraft and enabling defenders to align detection strategies with known techniques.
However, this approach presents significant structural limitations.
First, TTPs are not unique identifiers. Many techniques documented in ATT&CK are widely known, reused, or even commoditized. Adversaries frequently adopt publicly available tools, open-source frameworks, and malware-as-a-service offerings, resulting in multiple groups exhibiting identical or highly similar behaviors. Consequently, the presence of shared TTPs does not inherently indicate shared identity, but rather shared capability or access.

Second, adversaries are adaptive by design. Threat actors actively modify their TTPs to evade detection, respond to defensive improvements, or deliberately introduce false flags. This means that a group may significantly alter its observable behavior across campaigns, breaking continuity in traditional TTP-based attribution models. In such cases, rigid reliance on historical technique matching can lead to missed connections between related operations.
Campaign-Based Attribution
Campaign-based attribution represents a shift from static, group-centric thinking toward a more dynamic and evidence-driven model of adversary tracking. Rather than attempting to force continuity at the level of an APT label, this approach focuses on discrete campaigns time-bound clusters of activity that share a common objective, infrastructure set, and operational pattern.
A campaign can be defined as a coherent sequence of operations conducted within a specific timeframe, typically characterized by consistent targeting, tooling, and execution flow. Unlike broad group designations, campaigns reflect observable reality rather than inferred identity. This makes them a more reliable unit of analysis in environments where adversaries continuously evolve.
The key advantage of campaign-based attribution lies in its ability to handle change. As illustrated in the model above, activity is segmented into campaigns (e.g., Campaign A, B, C, D), each representing a distinct operational phase. While individual campaigns may differ in their TTPs, tooling, or infrastructure, they often exhibit partial overlaps across multiple dimensions. These overlaps rather than exact matches form the basis for linking activity over time.
Instead of asking:
“Does this activity match the known TTPs of Group X?”
Campaign-based attribution reframes the question as:
“How does this campaign relate to previous campaigns, and what evidence supports continuity?”
This model also reduces the risk of misattribution. Because it does not rely on a single dimension such as TTP similarity, it avoids the pitfalls of shared tooling and false flags. Instead, attribution becomes a multi-dimensional correlation problem, where confidence increases as more independent links are established between campaigns.
In practice, campaign-based attribution is often represented as a progression:
- Campaign A → Campaign B → Campaign C → Campaign D
Where each transition is supported by:
- Partial TTP overlap
- Infrastructure similarities
- Shared targeting patterns
- Consistent operational intent
Over time, these linked campaigns form a continuity narrative, allowing analysts to infer the presence of a persistent threat actor—even when individual components of their operations have changed.
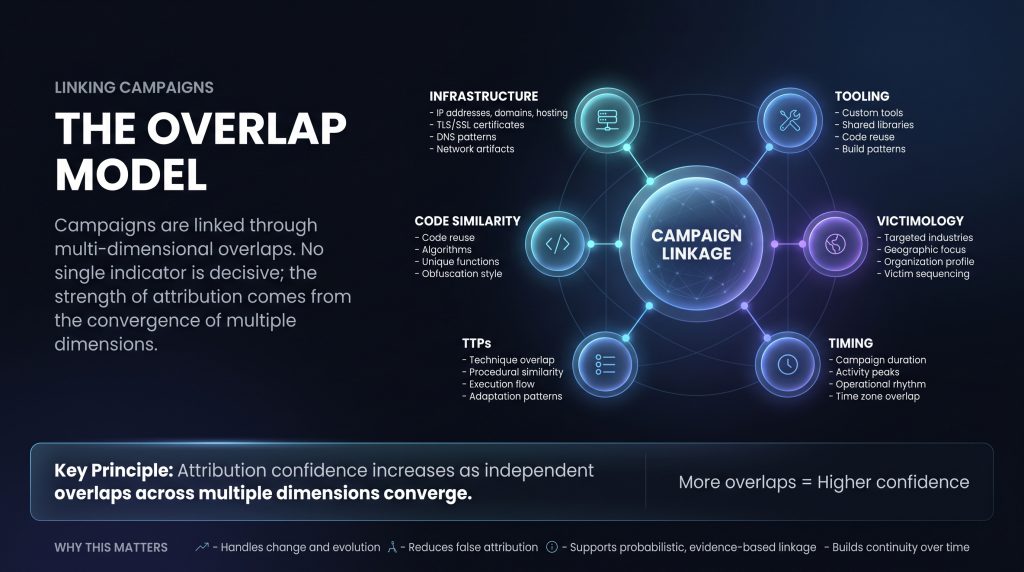
Linking Campaigns: The Overlap Model
A core challenge in campaign-based attribution is determining how seemingly distinct operations can be reliably connected over time. The overlap model addresses this by shifting the focus from single indicators to multi-dimensional correlation, where attribution emerges from the convergence of multiple independent signals rather than reliance on any one factor.
At its foundation, the overlap model assumes that no single artifact whether a tool, IP address, or technique—is sufficient to establish continuity. Instead, campaigns are linked through partial overlaps across several analytical dimensions, each contributing incrementally to the overall attribution confidence.
These dimensions typically include:
- Infrastructure: Shared or similarly structured infrastructure such as domain naming conventions, hosting patterns, TLS certificate reuse, or DNS behavior. Even when infrastructure is rotated, adversaries often exhibit consistent setup habits or operational preferences.
- Tooling: Reuse or evolution of malware families, loaders, or internal frameworks. This may include shared code libraries, similar build processes, or consistent development patterns across campaigns.
- Code Similarity: Overlaps in source code, algorithms, encryption routines, or obfuscation techniques. Even minor reuse such as function structures or error handling logic can provide strong linkage signals.
- TTPs (Tactics, Techniques, and Procedures): Procedural similarities in how operations are executed, including initial access methods, lateral movement strategies, and persistence mechanisms. While TTPs can change, adversaries often retain elements of their operational workflow.
- Victimology: Consistency in targeting patterns, such as specific industries, geographic regions, or organization types. Strategic intent is often one of the most stable indicators of continuity.
- Timing: Temporal patterns including campaign duration, activity cycles, working hours, or alignment with geopolitical events. These patterns can reveal underlying operational rhythms.
The strength of the overlap model lies in its combinatorial nature. Individually, each dimension may provide weak or ambiguous signals. However, when multiple dimensions align such as similar infrastructure setup, overlapping victim profiles, and consistent execution flow the likelihood of a shared origin increases significantly.
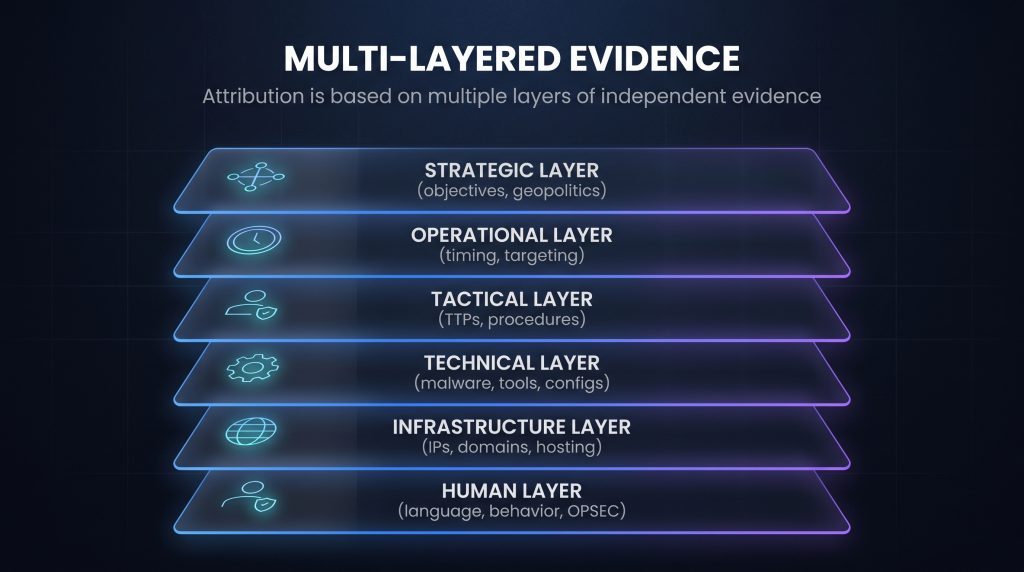
Multi-Layered Evidence
Effective attribution in cyber threat intelligence cannot rely on a single source of truth. Instead, it is built upon a multi-layered evidence model, where independent analytical layers contribute to a unified assessment. This approach acknowledges that adversary activity is complex and multi-faceted, and that reliable conclusions emerge only when multiple dimensions of evidence converge.
Each layer represents a different perspective of the adversary’s behavior, capabilities, and intent. Individually, these layers may provide incomplete or ambiguous signals; collectively, they form a robust and defensible attribution framework.
Strategic Layer
The strategic layer focuses on high-level intent and geopolitical alignment. It examines why an operation is conducted, including the choice of targets, alignment with national interests, and timing in relation to political or economic events. This layer is often one of the most stable over time, as underlying objectives tend to persist even when tactics change.
Operational Layer
The operational layer analyzes how campaigns are conducted over time. This includes targeting patterns, victim sequencing, campaign duration, and activity timing. For example, consistent working hours, regional focus, or repeated targeting of specific sectors can indicate a shared operational structure or mission set.
Tactical Layer
The tactical layer maps the procedural execution of attacks, often aligned with frameworks such as MITRE ATT&CK. It includes initial access techniques, persistence mechanisms, lateral movement, and data exfiltration methods. While TTPs are valuable, they must be interpreted carefully, as they can be modified or shared across multiple actors.
Technical Layer
The technical layer focuses on tools and malware characteristics, including custom implants, loaders, encryption routines, and configuration patterns. Code structure, development practices, and build artifacts can provide strong linkage signals, particularly when unique or proprietary elements are identified.
Infrastructure Layer
This layer examines the underlying infrastructure supporting operations, such as domains, IP addresses, hosting providers, TLS certificates, and DNS patterns. Even with rapid rotation, adversaries often exhibit consistent infrastructure management behaviors, which can be used to correlate campaigns.
Human Layer
The human layer captures operator-specific characteristics, including language artifacts, coding style, behavioral patterns, and operational security (OPSEC) practices. Mistakes, habits, and stylistic fingerprints can persist across campaigns, offering subtle but powerful indicators of continuity.
Convergence and Attribution Strength
The strength of attribution increases as evidence from these layers begins to align. A single matching indicator such as a reused IP address or technique—provides limited confidence. However, when multiple layers converge (e.g., shared victimology, similar tooling, consistent timing, and overlapping infrastructure patterns), the likelihood of a common origin becomes significantly higher.
This layered approach also mitigates the risk of false attribution. By requiring independent corroboration across multiple dimensions, analysts can distinguish between coincidental similarities and meaningful relationships.
Continuity Model: Campaign Linkage Graph
To operationalize campaign-based attribution and the overlap model, threat intelligence analysis can be formalized through a Campaign Linkage Graph a structured representation of how campaigns relate to one another over time. This model transforms attribution from a linear or label-based process into a graph-driven analytical framework, where continuity is derived from relationships rather than assumed identity.
In this model, each node represents a distinct campaign defined by its timeframe, objectives, tooling, and operational characteristics. The connections between these nodes, or edges, represent the degree of relatedness between campaigns. These relationships are not binary; instead, they are weighted based on the strength of overlapping evidence.
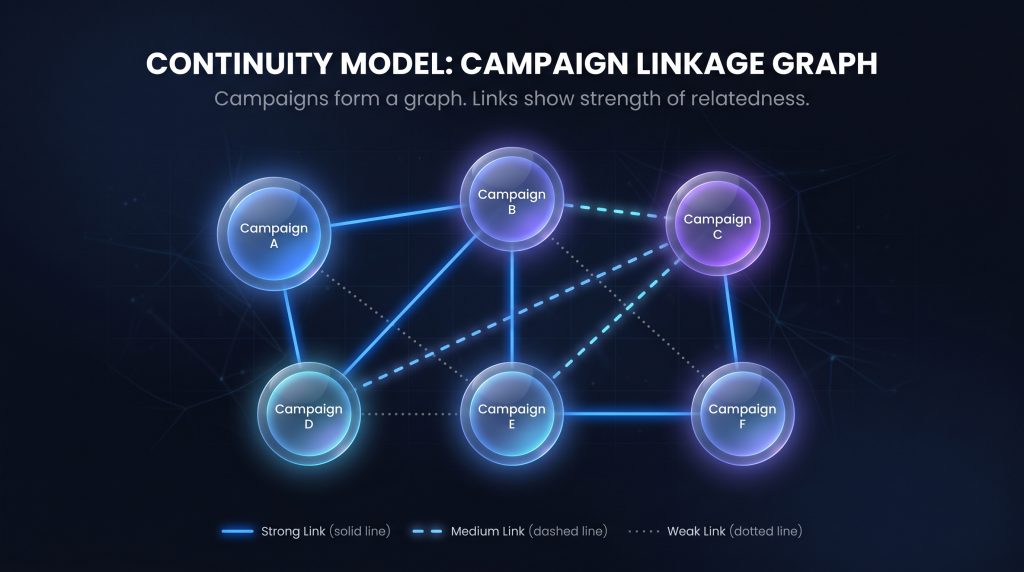
Graph Structure and Interpretation
Campaigns are connected through links that reflect varying levels of confidence:
- Strong Links indicate substantial overlap across multiple independent layers, such as shared infrastructure patterns, code similarities, consistent victimology, and aligned operational behavior.
- Medium Links represent partial overlap where some dimensions align, but alternative explanations remain plausible.
- Weak Links capture minimal or tentative similarities, often requiring further validation before being considered meaningful.
Continuity Through Connectivity
Rather than asking whether two campaigns are identical, the graph model asks:
“How strongly are these campaigns connected, and through which dimensions?”
This enables continuity to be established even when direct similarities are limited. For example, Campaign A may not strongly resemble Campaign D, but if both are strongly linked to Campaign B, an indirect relationship can be inferred. Over time, these chains of connections form a broader network that reflects the evolution of adversary activity.
Handling Evolution and Fragmentation
The Campaign Linkage Graph is particularly effective in addressing adversary evolution:
- Tooling changes are absorbed as new nodes with partial links to previous campaigns
- Infrastructure rotation appears as weaker but still traceable connections
- Operator changes may alter certain layers while preserving others (e.g., strategic intent or victimology)
- Splintering or collaboration can be visualized as branching or converging nodes within the graph
Analytical Advantages
The graph-based model provides several key benefits:
- Resilience to change: It does not require exact matches to maintain continuity
- Transparency: Relationships are explicitly represented and can be traced
- Scalability: New campaigns can be added without redefining existing structures
- Probabilistic reasoning: Confidence is derived from the density and strength of connections
From Groups to Graphs
Ultimately, this model reframes the concept of an APT group. Instead of being treated as a fixed entity, a group becomes an emergent property of the graph a cluster of strongly interconnected campaigns that share sufficient overlap across multiple dimensions.
Confidence-Based Attribution
Attribution in cyber threat intelligence is inherently probabilistic, not absolute. Unlike deterministic systems, where outcomes can be proven with certainty, adversary attribution operates under conditions of incomplete visibility, evolving behaviors, and potential deception. As a result, conclusions must be expressed in terms of confidence levels, reflecting the strength, consistency, and independence of the underlying evidence.
The confidence-based model builds directly on the principles of multi-layered evidence and campaign linkage. Rather than forcing a binary judgment correct or incorrect it allows analysts to quantify the reliability of their assessment based on how strongly different dimensions align across campaigns.

High Confidence
High-confidence attribution is achieved when there is strong, consistent, and multi-layered overlap across campaigns. This typically includes:
- Convergence across multiple independent evidence layers (strategic, operational, technical, infrastructure, human)
- Repeated patterns observed across different timeframes
- Minimal plausible alternative explanations
At this level, the relationship between campaigns is well-supported, and the likelihood of a shared origin is considered highly probable. While absolute certainty is never claimed, the assessment is robust and defensible.
Medium Confidence
Medium-confidence attribution reflects partial overlap across several dimensions, but with some degree of ambiguity. In these cases:
- Certain indicators align (e.g., similar tooling or victimology), but not consistently across all layers
- Evidence may be limited in scope or timeframe
- Alternative explanations such as shared tools or coincidental targeting remain plausible
This level requires cautious interpretation. While there are meaningful signals of continuity, the assessment should be treated as indicative rather than conclusive, often requiring further data to strengthen or refute the linkage.
Low Confidence
Low-confidence attribution is assigned when there is limited, weak, or inconclusive evidence. This may occur when:
- Only a single dimension shows similarity (e.g., one shared TTP or infrastructure element)
- Observed overlaps are common across multiple unrelated actors
- Data is insufficient, fragmented, or lacks validation
At this level, attribution should be considered tentative, and strong claims should be avoided. It serves more as a hypothesis than a conclusion.
Conclusion
Attribution in modern cyber threat intelligence can no longer rely on the assumption that adversary groups are static, well-defined entities. As demonstrated throughout this research, threat actors evolve continuously adapting their tooling, modifying their TTPs, rotating infrastructure, and even changing operational personnel. This dynamic nature introduces a fundamental challenge to traditional attribution models, which often depend on rigid mappings and historical consistency.
By reframing attribution through the lens of campaigns rather than groups, a more accurate and resilient analytical model emerges. Campaigns provide a grounded, observable unit of analysis, allowing investigators to track real-world activity without forcing continuity where it may not explicitly exist. Through the use of the overlap model and multi-layered evidence, relationships between campaigns can be identified based on partial but meaningful correlations across strategic, operational, technical, and human dimensions.
The introduction of the Campaign Linkage Graph further strengthens this approach by structuring attribution as a network of relationships rather than a linear classification problem. In this model, continuity is not assumed it is inferred through evidence, weighted by the strength and diversity of overlaps. This enables analysts to capture not only persistence, but also evolution, fragmentation, and convergence within adversary operations.