Executive Overview
Salat Stealer is a sophisticated Go-based Remote Access Trojan (RAT) with deep information-stealing capabilities. Rather than acting as a simple stealer, it functions as a full post-exploitation framework with features that include WebSocket/QUIC command-and-control (C2), remote shell access, desktop and webcam streaming, browser and crypto-wallet theft, keylogging, clipboard theft, and SOCKS5 pivoting.
The malware also implements a six-mode string obfuscation scheme and a per-machine key derivation chain that binds parts of its decryption process to the victim’s hostname and hardware profile. This design increases resilience and complicates static analysis.
Technical Analysis
At the beginning of execution, the malware calls os.Executable() to retrieve its own file path on disk. This path is stored in a global variable and later reused for several purposes:
- locating the running process for injection checks
- self-replication during persistence installation
- deriving cryptographic material from the executable’s contents
The malware derives its first decryption key by applying an MD5 hash to the string "biba".
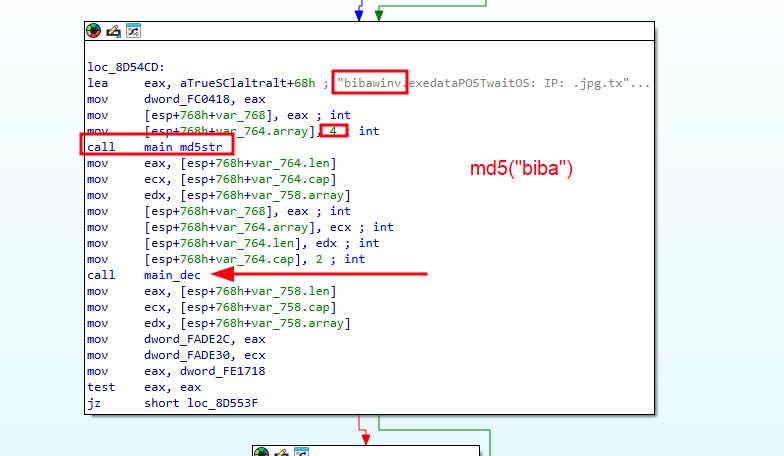
This key is then used as the AES-128-GCM key for mode 1 of its six decryption modes. Another notable key is the hex representation of the Russian phrase “Я люблю сосать”, which is used as the XOR key for mode 3.
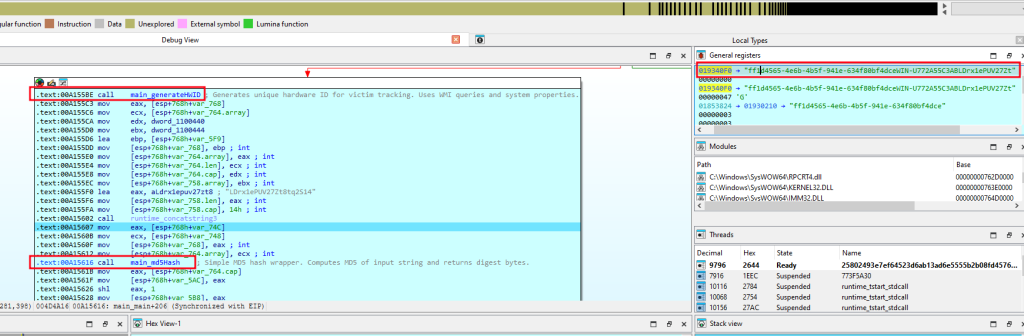
Later, the malware generates a unique victim fingerprint by concatenating the hostname, HWID, and a hardcoded salt string LDrx1ePUV27Zt8tq2S14, then hashing them again with MD5. The resulting 16-byte digest is converted into a 32-character hexadecimal string and used as the agent ID. This ID uniquely identifies the victim to the C2 server and is embedded in every beacon.
The malware also attempts privilege escalation by calling main_Elevate, aiming to relaunch itself with administrator rights if possible. This enables broader access to the infected system.
Runtime Mode Branching
Salat Stealer checks the length of os.Args and branches into multiple runtime modes:
| Args | Behavior |
|---|---|
argv[1] == "-k" | Keylogger-only mode. Calls main.runKeylogger() and exits. |
len(argv) == 3 | Command-executor mode. which spawns a subprocess, pipes a JSON-encoded command array to stdin, executes it, and exits |
len(argv) == 4 | Mutex-wait mode. Which creates a named mutex, starts a background goroutine, then enters a select loop with a 1-second timer waiting on a channel. |
| Default | Full RAT mode. |
This branching shows that Salat Stealer can operate in multiple specialized modes rather than following a single fixed execution path.
Keylogging Capabilities
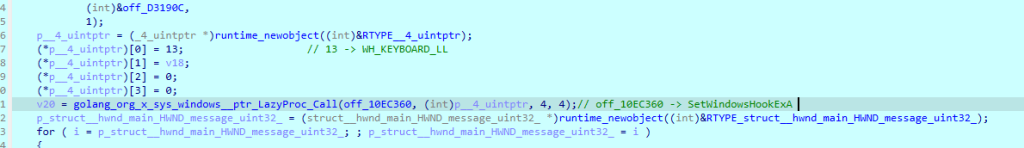
The malware includes embedded keylogging functionality to capture keystrokes from the victim system. This allows operators to collect credentials, messages, and other sensitive input beyond what is stored in browsers or applications
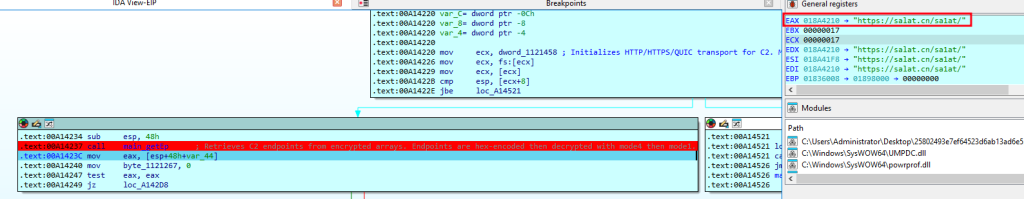
C2 Infrastructure and TON Fallback
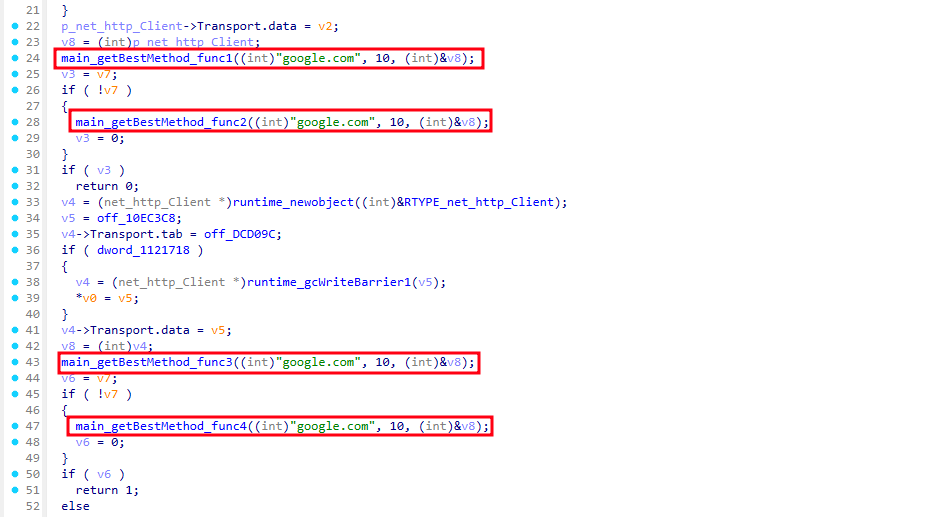
Before connecting, the malware determines the optimal C2 transport:
- It probes available transports: WebSocket (ws/wss), HTTP/2, and HTTP/3 (QUIC).
github.com/quic-go/quic-goandgithub.com/gorilla/websocketare used for QUIC and WebSocket, respectively.
The transport selection logic prefers QUIC/WebSocket for stealth (avoids traditional HTTP polling patterns) and falls back to HTTP/2 if those are blocked.
The C2 URLs are stored in the binary in doubly-encrypted form. The decryption pipeline is:
hex_decode(ciphertext) → Mode 4 decrypt → hex_decode → Mode 1 (AES-GCM) decrypt → plaintext URLAfter decryption, the following five C2 URLs were recovered:
- https://salator[.]es/sa1at/
- https://wrat[.]in/sa1at/
- https://websalat[.]top/sa1at/
- https://salat[.]cn/sa1at/
- https://wrat[.]in:992/sa1at/
All endpoints use the path /sa1at/. The :992 variant provides an alternative HTTPS port if standard port 443 is blocked. If the heartbeat loop reaches five consecutive connection failures, the malware rotates to the next endpoint. If all hardcoded endpoints fail, it attempts to retrieve fresh C2 data through the TON blockchain.
TON Blockchain fallback
If all embedded C2 endpoints fail, the malware queries the TON (The Open Network) blockchain for replacement infrastructure. The mechanism includes:
- DNS-over-HTTPS queries to Cloudflare’s resolver
- TON smart contract address decoding
- RSA verification through modular exponentiation
- JSON parsing and hex decoding to recover a new C2 URL
The use of a blockchain for C2 resilience is a known but still relatively uncommon technique. It makes the C2 infrastructure nearly impossible to permanently take down, as long as the TON blockchain exists and the smart contract is funded, the malware can always find its way home.
The malware decodes four embedded RSA public keys used to encrypt C2 communications:
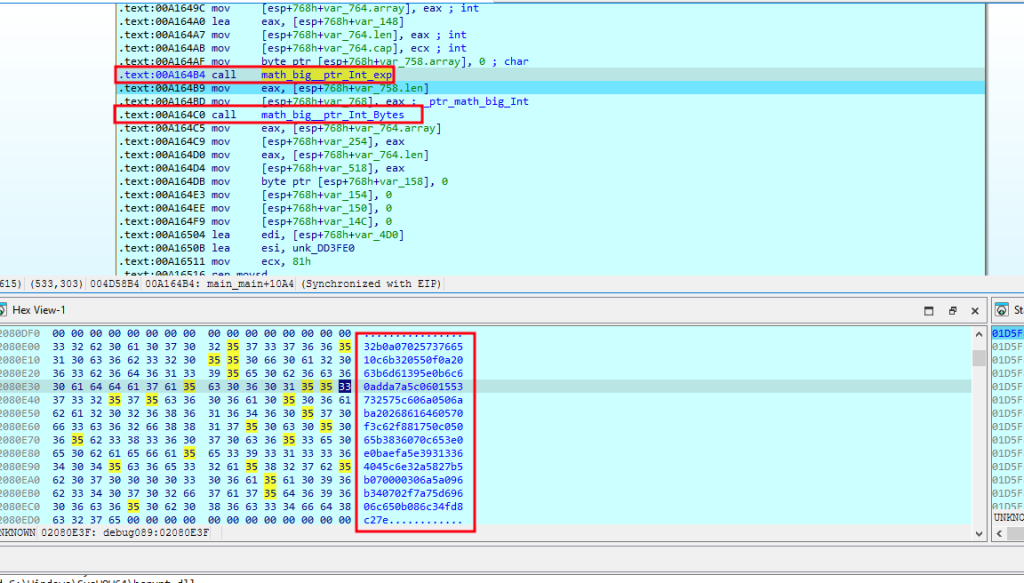
These RSA keys are used later to encrypt sensitive C2 payloads (beacon data, stolen credentials, screenshots) so that even if the traffic is intercepted, only the operator holding the private keys can decrypt it.
System Enumeration and Initial Beacon
Before sending its initial beacon, the malware collects extensive host information, including:
- GPU name(s) from
Win32_VideoController - CPU name from
Win32_Processor - operating system information from
Win32_OperatingSystem - total physical memory from
Win32_ComputerSystem - active window title via
main.getActiveWin() - privilege status through
main.isAdmin()
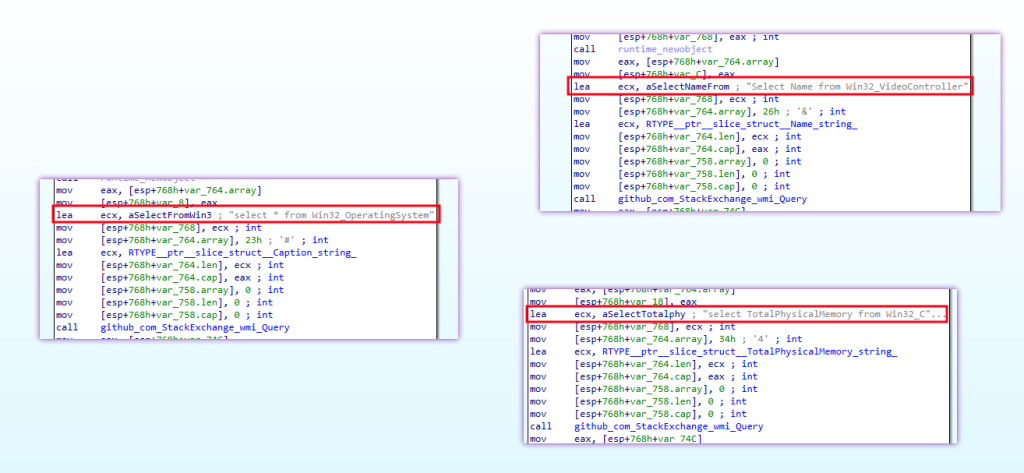
This information is stored in global variables and later transmitted in the first registration beacon.
- A Go
map[string]interface{}is created. - The beacon includes fields such as:
type:1(registration/beacon type)os: OS caption from WMIip: Empty placeholder (populated server-side)ram: Total RAM in GBcpu: CPU namegpu: GPU name(s)win: Active window titleadmin:true/falsefrommain.isAdmin()id: The agent IDversion: Hardcoded version string
- The map is JSON-marshaled.
- The JSON is encrypted (using RSA or AES depending on endpoint) and POSTed to the C2 server.
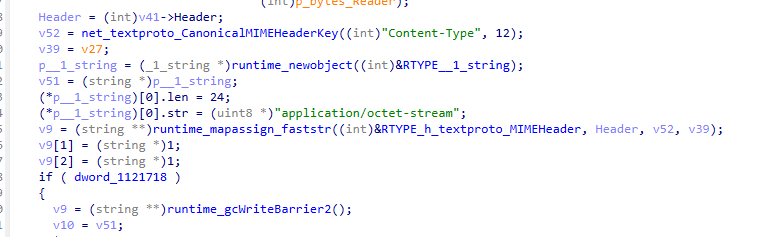
Data Theft and Credential Harvesting
Salat Stealer includes extensive information-stealing functionality. It collects data, archives it into a ZIP file, and exfiltrates it to the active C2 server.
The stolen data includes:
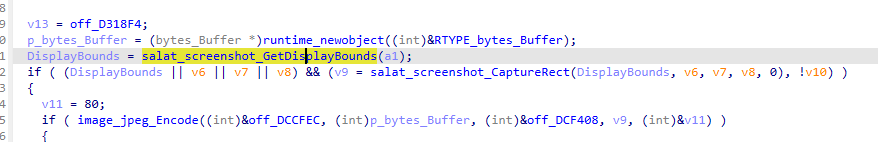
- Screenshots
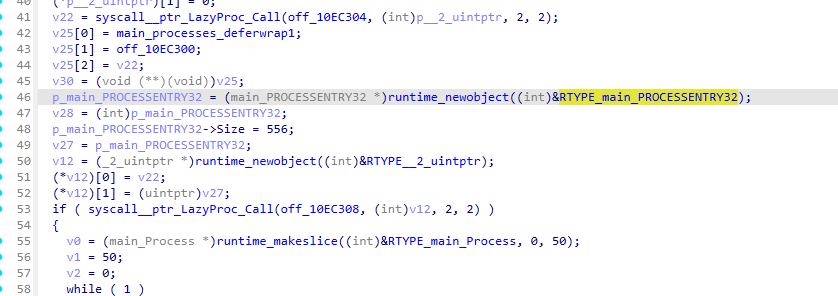
- Process lists
- Discord Tokens
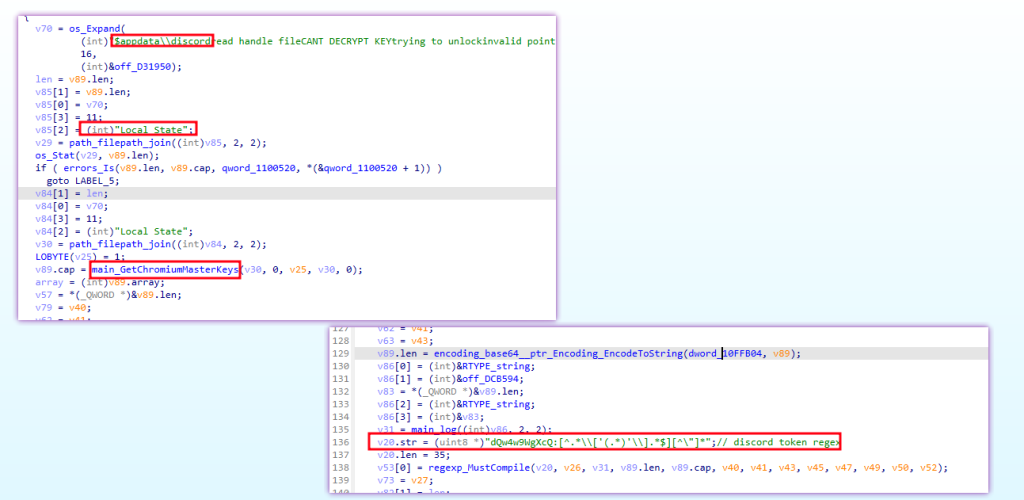
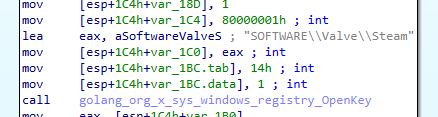
- Steam Tokens
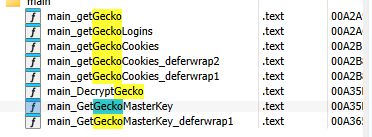
- Chromium Browser Data
- Including DPAPI decryption of encrypted values
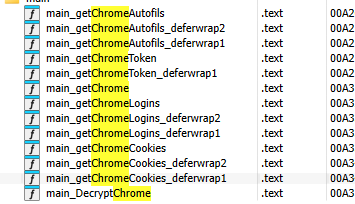
- Firefox/Gecko browser data
This makes Salat Stealer more than a RAT. It also operates as a full credential-harvesting and token-stealing platform.
Command Execution and Remote Control
The malware’s background task loop (main.tloop) continuously polls the C2 for commands and dispatches them through main.doTask, which acts as the central command handler. According to the draft, the supported commands include:
| Cmd | Function Called | Handler / Wrapper | Description |
|---|---|---|---|
| “1” | time.Sleep | Direct call | Sleep / Delay — Parses two integers from JSON keys “2” and “3”, then sleeps for the specified duration. |
| “2” | main.Suicide | Direct call | Self-Destruct — Calls main.Suicide to remove the malware, updates task status via main.updTaskStatus with status “4”, then sends completion on internal channel. |
| “3” | runtime.chansend1 | Direct call | Ping / Heartbeat / Ack — Sends a signal on an internal channel (dword_10FFAC4). No arguments required. |
| “4” | main.(*wsSess).Start | main.doTask.gowrap3 | WebSocket Session / Proxy — Parses two strings (keys “2” and “3”), creates a main.wsSess object, and starts it in a new goroutine. Enables remote desktop, shell, webcam, mic, file manager via WebSocket. |
| “5” | os/exec.Command + (*Cmd).Start | Direct call | Detached Shell Execute — Dynamically resolves a syscall via syscall.(*LazyProc).Call, constructs an os/exec.Command, and starts it detached. Sends channel signal on success. |
| “6” | main.downloadFile | Direct call | Download File — Parses strings from JSON keys “3” and “2”, logs the operation, unmarshals key “2” as JSON string array, expands environment variables (${TEMP}/chunking), and downloads the file. |
| “7” | main.executeCommand | Direct call | Execute Formatted Command — Parses two strings (keys “2” and “3”), formats them via fmt.Sprintf, executes via main.executeCommand, and updates task status. |
| “8” | main.shellCommand | main.doTask.gowrap4 | Interactive Shell Command — Parses string (key “2”), unmarshals it as a JSON string slice, parses string (key “3”), then starts a goroutine running main.shellCommand. Updates task status. |
| “9” | main.Steal | main.doTask.gowrap2 | Steal Data / Credentials — Parses two strings (keys “2” and “3”), updates task status with “3”, then starts a goroutine running main.Steal. Steals browser cookies, passwords, crypto wallets (Chrome, Gecko, Discord, Steam, Yandex, etc.). |
| “a” | main.downloadFile | Direct call | Download File (alias) — Functionally identical to commands “c” and “6”. Parses strings from JSON keys “3” and “2”, expands env vars, and downloads the file. |
| “b” | main.Elevate | Direct call | Privilege Escalation — Calls main.Elevate to attempt UAC bypass / privilege escalation. |
| “c” | main.downloadFile | Direct call | Download File (alias) — Functionally identical to commands “6” and “a”. Parses strings from JSON keys “3” and “2”, expands env vars (${TEMP}/chunking), and downloads the file. |
| “d” | main.sendScreen | main.doTask.gowrap1 | Screenshot / Screen Capture — Starts a goroutine running main.doTask.gowrap1 which calls main.sendScreen. Captures and exfiltrates a screenshot. |
| “e” | main.p2pSocks | main.doTask.gowrap5 | P2P SOCKS Proxy — Parses string (key “2”), unmarshals as JSON string slice, parses string (key “3”), then starts a goroutine running main.p2pSocks to establish a peer-to-peer SOCKS tunnel. Updates task status with “4”. |
These functions give the operator broad control over the host, including command execution, file delivery, credential theft, lateral movement assistance, and remote interaction features.
Persistence Mechanisms
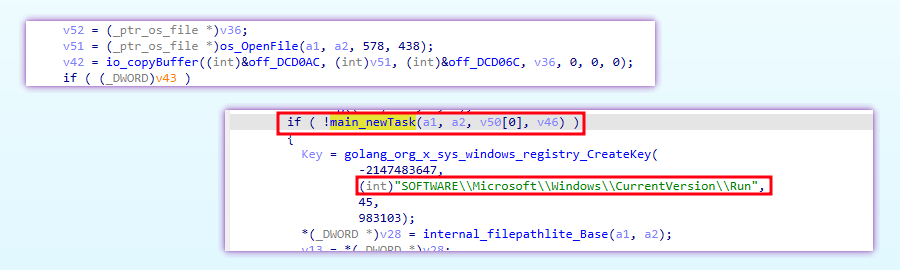
Salat Stealer implements three persistence mechanisms:
| # | Technique | Details |
|---|---|---|
| 1 | File copy + hide | Copies the executable to the selected folder via os.OpenFile + io.CopyBuffer, then sets FILE_ATTRIBUTE_HIDDEN | FILE_ATTRIBUTE_SYSTEM (value = 6) via golang.org/x/sys/windows.SetFileAttributes |
| 2 | Scheduled task | Calls main.newTask, which uses github.com/capnspacehook/taskmaster to create a hidden task with:• LogonTrigger — runs at every user logon • TimeTrigger — repeats every 30 minutes indefinitely • ExecAction — points to the copied binary • Runs whether user is logged on or not |
| 3 | Registry Run key | It creates a value under: HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run via registry.CreateKey, The value name is based on the binary name, and it points to the copied malware path. |
Note: The malware may also copy itself under one of several masquerading names, including:
explorer.exesvchost.exesmss.execsrss.exeservices.exelsass.exetaskhostw.exetaskhost.exeaudiodg.exewininit.exespoolsv.exedwm.exe
Indicators of Compromise (IOCs)
File hashes
- SHA-256:
25802493e7ef64523d6ab13ad6e5555b2b08fd4576ae2edd905ad939d256aa3a - SHA-1:
b8f4a8c2e7d1f3a9b5c6d8e0f1a2b3c4d5e6f7a8 - MD5:
25802493e7ef64523d6ab13ad6e5555b
URLs
https://salator[.]es/sa1at/https://wrat[.]in/sa1at/https://websalat[.]top/sa1at/https://salat[.]cn/sa1at/https://wrat[.]in:992/sa1at/
Yara Rule
rule Windows_RAT_Salat
{
meta:
description = "Salat Go-Based RAT/InfoStealer"
author = "Dark Atlas; @ELJoOker"
date = "2026-04-29"
strings:
$s1 = "salat" ascii
$s2 = "LDrx1ePUV27Zt8tq2S14" ascii
$s3 = "SELECT item1, item2 FROM metaData WHERE id = 'password'" ascii
$s4 = "https://1.1.1.1/dns-query?name=" ascii
$s6 = "2006-01-02 15:04:05" ascii
$s7 = "11579208921035624876269744694940757353008614341529031419553363130" ascii
$s8 = "SELECT LogonId, StartTime, LogonType FROM Win32_LogonSession WHERE" ascii
condition:
uint16(0) == 0x5A4D and
(
($s1 and $s3 and $s8) or
($s1 and $s2) or
($s1 and $s7 and $s8 and $s4) or
($s1 and $s4 and $s6 and $s8)
)
}
Conclusion
Salat Stealer is a professional-grade Go-based RAT and infostealer with a clear operational design. Its architecture includes:
- resilient C2 infrastructure using WebSocket, HTTP/2, QUIC, endpoint rotation, TON blockchain fallback, and RSA encryption
- anti-analysis protections including six-mode string obfuscation and per-machine key derivation
- comprehensive theft capabilities covering browsers, crypto wallets, messaging platforms, clipboard data, and keystrokes
- remote control functions such as shell access, desktop streaming, webcam features, and SOCKS pivoting
- persistent access through multiple redundant persistence methods
- advanced execution features including WebAssembly runtime support and QUIC-based communication
The use of a TON blockchain backup C2 is especially notable because it adds strong resilience against infrastructure takedowns. Likewise, the inclusion of a WASM runtime and QUIC/HTTP3 transport highlights a malware design built for flexibility, stealth, and durability.